Synopsis
This post will discuss how to structure your Hiera Data, so that your profiles will automatically inject the parameters.
Why? So we can keep our profile classes and other classes super clean and succinct.
If you have If else statements in your classed depending on what environment or node the code is running on, you might have a code structure smell. Lets dig in.
Assumptions
You are using a Puppet Control Repository and leveraging Code Manager (R10K) to manage your code with Puppet Enterprise
Secondly you are using Profiles and Roles pattern to structure your classes.
I highly recommend you download the Puppet Control Repository template here.
Profiles and Roles
The most important aspect to consider is structuring your Profiles and Roles to accept parameters that can be resolved and matched to Hiera Data.
Here we have a role for all our Jumpboxes that we can use to remote into.
As we can see it will have the following profiles applied:
class role::jumpbox {
include profile::base
include profile::jumpbox::jumpboxsoftware
include profile::jumpbox::firewall
include profile::jumpbox::hosts
}
Lets pick one of these profiles that require data from Hiera.
class profile::jumpbox::hosts (
String $hostname = 'changeme',
String $ip = 'changeme',
)
{
host { $hostname:
ensure => present,
ip => $ip,
}
}
The above profile ensures that the /etc/hosts file has some entries in it.
It accepts two parameters:
profile::jumpbox::hosts::ip
profile::jumpbox::hosts::hostname
Similar to Java or C# we can use a sort of dependency injection technique, where puppet will automatically look for this parameter in Hiera; a key/value store.
Hiera
The trick is to structure your Hiera Data and use the same Fully Qualified Names in the keys.
Each environment needs a different set of host names.
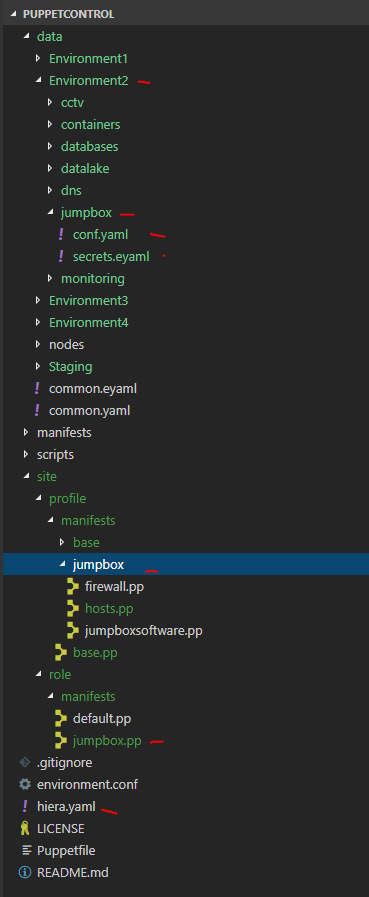
I then have the following structure in the control repro
.data\<environment1>\jumpbox\conf.yaml
.data\<environment2>\jumpbox\conf.yaml
.data\<environment3>\jumpbox\conf.yaml
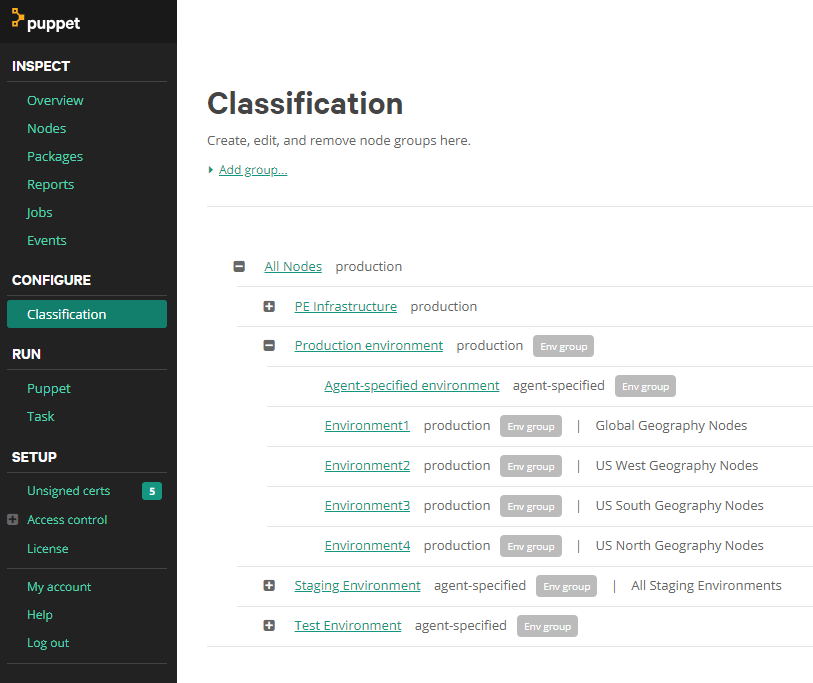
Each folder in data represents an Environment in Puppet Classifications:
The second important convention is we use a geography variable in each Environment to resolve Hiera Data automatically.
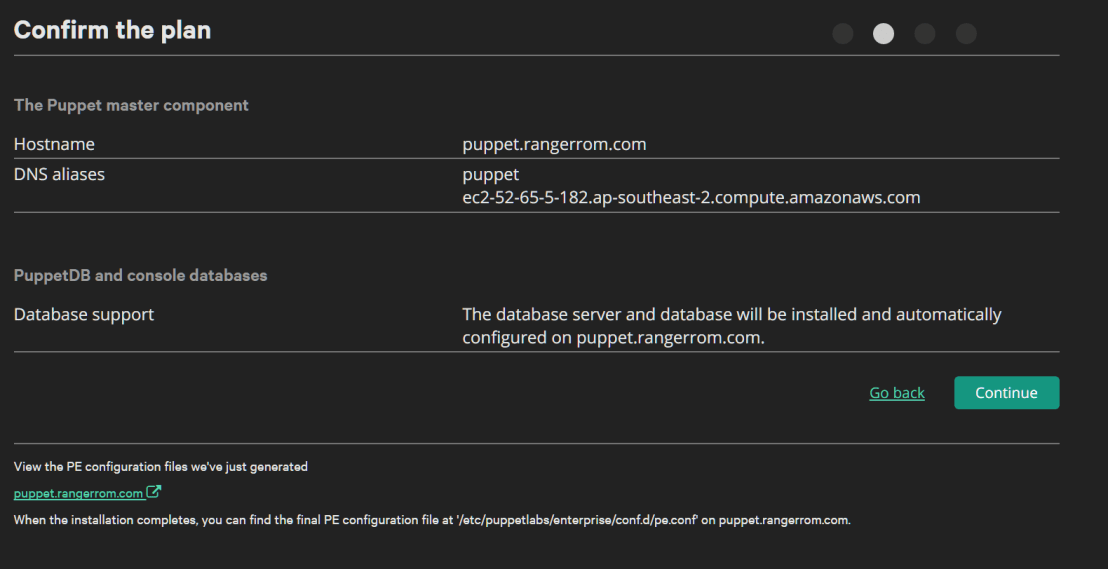
Go to your Puppet Master Enterprise Web Console and manage the Classifications.
What you are doing is creating a variable that can be used by the hiera.yaml file to dynamically load data for the correct environment when the agent runs.
On the Puppet Master we need to setup our environments to match the Control Repository and add the magic variable. Any Node that runs the puppet agent will then have this variable set. This can then be used to load the corresponding Hiera config file.
Here we can see Environment1 has a variable defined called geography that matches the Environment name. We can then leverage this convention:
Puppet Profile -> Hiere Data lookup -> Folder that matches the variable name -> resolve parameter
This is all done automatically for you.
Puppet Control Repository Structure
The repository then looks like this:
Let us dig a little deeper and see how this structure is configured.
hiera.yaml
.\hiera.yaml
This file now contains the instructions to tell Hiera how to load our data.
—hiera.yaml—
---
version: 1
defaults:
datadir: "data"
hierarchy:
- name: 'Yaml Key Value Store'
data_hash: yaml_data
paths:
- "%{geography}/jumpbox/conf.yaml"
- "common.yaml"
- name: "Encrypted Data"
lookup_key: eyaml_lookup_key
paths:
- "%{geography}/jumpbox/secrets.eyaml"
- "common.eyaml"
options:
pkcs7_private_key: /etc/puppetlabs/puppet/eyaml/private_key.pkcs7.pem
pkcs7_public_key: /etc/puppetlabs/puppet/eyaml/public_key.pkcs7.pem
Data – yaml
the .yaml files will contain the same variable names (fully qualified) that match the PROFILE files e.g.
—conf.yaml—
profile::jumpbox::hosts::hostname: 'rdp.rangerrom.com'
profile::jumpbox::hosts::ip: 8.8.8.8'
As you can see above. As long as your profiles and parameters match, Hiera will automatically inject the correct parameter for each environment.
Hiera will resolve – %{geography}/jumpbox/conf.yaml
In the Puppet master you had setup your classifications, so when the puppet agent runs on Environment1 nodes, it will get the jumpbox/conf.yaml that matches the variable name geography=”Environment1″
Encrypted Data – eyaml
Encrypted data is just as easy to store.
* Generate the encrypted data.
* Store the data in an eyaml file in the same folder as the yaml data.
* Add a path to the data in the hiera.yaml file.
We have encrypted data e.g. the default local admin account setup via the profile – include profile::base
We use the Puppet Master private key to generate the encrypted data, see the end of this blog on how to create encrypted data.
—secrets.eyaml—
profile::base::adminpassword: >
ENC[PKCS7,MIIBeQYJKoZIhvcNAQcDoIIBajCCAWYCAQAxggEhMIIBHQIBADAFMAACAQEw
DQYJKoZIhvcNAQEBBQAEggEAnMWlddVoU9lC8tBNvOLI9OYI6xtCD0y3NIVe
Ylm25dUZ8sqGP+yVQ8Y0P5xIse5f/WVOkavByZJK5yV4fDYFpD6IhXk4IJUe
dVUw8VmO/RG84AknDDrtNPlSPm4uQqYPOOa0BmgO1iiOY4rcAxhFzT5nzod3
MIK7lmbuP859R5jtJ5PZxZKCNERGY+dxUZfcdPs0/zr/KgLGcHc/awzYtEuI
0tOGPp80gTVkhmCHO7KuClsg97XTRGi0BfiuiyjOWLIeAx5hbhMHi65ZPl5U
MlJFoTA1nw3ATcC6NL3ikECWaQrt2xyxZ1uoYKqvN0ClsFLIqBQ1gXRTvQPD
SlBQqDA8BgkqhkiG9w0BBwEwHQYJYIZIAWUDBAEqBBCWLuT77kT6q/ojfjKx
wk17gBATvEM58mGyP5CGbMqlbEip]
How to Encrypt Data
SSH into the Puppet Master. Locate your Puppet Master Certificates. Then run the following
puppetmaster@rangerrom.com:~$ sudo /opt/puppetlabs/puppet/bin/eyaml encrypt -p --pkcs7-public-key=/etc/puppetlabs/puppet/eyaml/public_key.pkcs7.pem
Enter password: ***
string: ENC[PKCS7,MIIBeQYJKoZIhvcNAQcDoIIBajCCAWYCAQAxggEhMIIBHQIBADAFMAACAQEwDQYJKoZIhvcNAQEBBQAEggEAnMWlddVoU9lC8tBNvOLI9OYI6xtCD0y3NIVeYlm25dUZ8sqGP+yVQ8Y0P5xIse5f/WVOkavByZJK5yV4fDYFpD6IhXk4IJUedVUw8VmO/RG84AknDDrtNPlSPm4uQqYPOOa0BmgO1iiOY4rcAxhFzT5nzod3MIK7lmbuP859R5jtJ5PZxZKCNERGY+dxUZfcdPs0/zr/KgLGcHc/awzYtEuI0tOGPp80gTVkhmCHO7KuClsg97XTRGi0BfiuiyjOWLIeAx5hbhMHi65ZPl5UMlJFoTA1nw3ATcC6NL3ikECWaQrt2xyxZ1uoYKqvN0ClsFLIqBQ1gXRTvQPDSlBQqDA8BgkqhkiG9w0BBwEwHQYJYIZIAWUDBAEqBBCWLuT77kT6q/ojfjKxwk17gBATvEM58mGyP5CGbMqlbEip]
OR
block: >
ENC[PKCS7,MIIBeQYJKoZIhvcNAQcDoIIBajCCAWYCAQAxggEhMIIBHQIBADAFMAACAQEw
DQYJKoZIhvcNAQEBBQAEggEAnMWlddVoU9lC8tBNvOLI9OYI6xtCD0y3NIVe
Ylm25dUZ8sqGP+yVQ8Y0P5xIse5f/WVOkavByZJK5yV4fDYFpD6IhXk4IJUe
dVUw8VmO/RG84AknDDrtNPlSPm4uQqYPOOa0BmgO1iiOY4rcAxhFzT5nzod3
MIK7lmbuP859R5jtJ5PZxZKCNERGY+dxUZfcdPs0/zr/KgLGcHc/awzYtEuI
0tOGPp80gTVkhmCHO7KuClsg97XTRGi0BfiuiyjOWLIeAx5hbhMHi65ZPl5U
MlJFoTA1nw3ATcC6NL3ikECWaQrt2xyxZ1uoYKqvN0ClsFLIqBQ1gXRTvQPD
SlBQqDA8BgkqhkiG9w0BBwEwHQYJYIZIAWUDBAEqBBCWLuT77kT6q/ojfjKx
wk17gBATvEM58mGyP5CGbMqlbEip]
puppetmaster@rangerrom.com:~$








You must be logged in to post a comment.